West virginia digital
https://westvirginiadigitalnews.com
administrator
- Total Post (47816)
- Comments (11)
Articles By This Author

February’s Most Loved Finds – Julia Berolzheimer
- By West virginia digital
- . February 26, 2025
Outfit Details:Rosie Assoulin Top & Skirt (more sizes here), Hermes Bangles (similar here, less expensive here), Morely Dresses on C & M February’s most-loved finds capture

Ancient DNA Sheds New Light On The Link Between The European Huns And The Xiongnu Empire
- By West virginia digital
- . February 26, 2025
Conny Waters – AncientPages.com – In the 370s, the Huns made a sudden appearance in Europe, establishing a significant yet
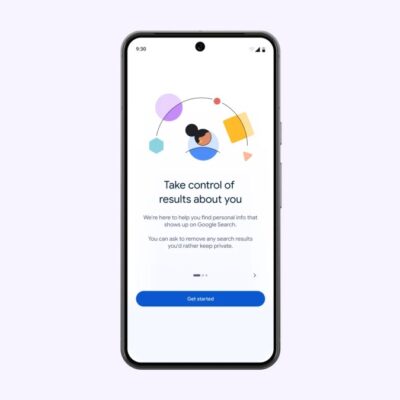
Google makes it easier to delete personal info from Search results
- By West virginia digital
- . February 26, 2025
Google announced on Wednesday that it’s updating its “Results about you” tool to make it easier for users to protect

Microsoft finalizes its EU sovereign cloud project
- By West virginia digital
- . February 26, 2025
Microsoft says that it has completed a multi-year project to allow Europe-based customers using its cloud services to store and

Bridgetown Research raises $19M to speed up due diligence with AI
- By West virginia digital
- . February 26, 2025
Due diligence is a costly business, and not just in the realm of investing. Even for a company trying to

Lock screen platform Glance launches AI-powered shopping experience, gets fresh backing from Google
- By West virginia digital
- . February 26, 2025
Lock screen platform Glance announced today that it is launching a new generative AI-based shopping experience. It will suggest different

Stanley Tucci Pasta Casserole | The Recipe Critic
- By West virginia digital
- . February 26, 2025
This website may contain affiliate links and advertising so that we can provide recipes to you. Read my disclosure policy.

Fulani: Africa’s Pastoralists Traced To Green Sahara Period,12,000 – 5,000 Years Ago
- By West virginia digital
- . February 26, 2025
Eddie Gonzales Jr. – AncientPages.com – Researchers identified a genetic component in all Fulani populations, suggesting a shared ancestry possibly

Regie.ai injects sales enablement with AI, but keeps humans in the loop
- By West virginia digital
- . February 26, 2025
There’s no sure-fire approach to sales enablement, the process of providing a sales team with the resources it needs to

Anagram takes a gamified approach to employee cybersecurity training
- By West virginia digital
- . February 26, 2025
Despite employers requiring their employees to complete yearly cybersecurity training courses, human-driven cybersecurity breaches still happen. The problem could even

